大屏Miracast投屏首次失败需重试定位总结
一、问题现象
在大屏项目打开Miracast投屏应用后,使用手机进行无线投屏时,首次投屏大概率失败,必须重试1~2次才能成功投屏。
- 问题概率:4/5(高概率复现)
- 影响范围:主要表现为首次投屏连接失败,重试后可成功
- 失败表现:手机搜索到设备并尝试连接,但最终超时或断开,无法建立投屏会话
二、分析过程
1. 初步分析(日志分析)
从日志分析,底层的P2P流程是正常的,连接已经成功建立:
1.1 启动GO
01-19 17:29:48.258 2211 3201 D C01560/WifiWpaHal: wpa recv buf: <3>P2P-GROUP-STARTED p2p0 GO ssid="DIRECT-9c-GK6320-miracast" freq=5180 passphrase="mTfcHSMx" go_dev_addr=fa:ab:4d:79:72:93 [PERSISTENT]!
01-19 17:29:48.258 2211 3201 D C01560/WifiWpaHal: wpa p2p callback p :P2P-GROUP-STARTED p2p0 GO ssid="DIRECT-9c-GK6320-miracast" freq=5180 passphrase="mTfcHSMx" go_dev_addr=fa:ab:4d:79:72:93 [PERSISTENT]!
01-19 17:29:48.258 3182 3183 I C05200/wpa_supplicant: P2P-GROUP-STARTED p2p0 GO ssid="DIR*******************ast" freq=5180 go_dev_addr=fa:ab:**:**:**:93 [PERSISTENT]
01-19 17:29:48.258 3182 3183 I C05200/wpa_supplicant: P2P: Storing credentials for a persistent group (GO Dev Addr fa:ab:**:**:**:93)
01-19 17:29:48.258 2211 3201 I C01560/WifiHalCallback: P2p group started event groupIfName: p2p0
01-19 17:29:48.258 3182 3183 I C05200/wpa_supplicant: P2P: Create a new persistent group entry
1.2 WPS交互成功
01-19 17:29:53.674 3182 3183 D C05200/wpa_supplicant: WPS: Probe Request for PBC received from d2:69:**:**:**:65
01-19 17:29:53.674 3182 3183 D C05200/wpa_supplicant: WPS: UUID-E from Probe Request - hexdump(len=16): c7 d9 6a fb fa bd 5e 24 8f d7 3b d7 12 5e 38 d6
01-19 17:29:53.674 3182 3183 D C05200/wpa_supplicant: WPS: Checking active PBC sessions for overlap
01-19 17:29:53.674 3182 3183 D C05200/wpa_supplicant: WPS: Add one for the requested UUID
01-19 17:29:53.674 3182 3183 D C05200/wpa_supplicant: WPS: Requested UUID - hexdump(len=16): c7 d9 6a fb fa bd 5e 24 8f d7 3b d7 12 5e 38 d6
01-19 17:29:53.674 3182 3183 D C05200/wpa_supplicant: WPS: Consider PBC session with d2:69:**:**:**:65
01-19 17:29:53.674 3182 3183 D C05200/wpa_supplicant: WPS: UUID-E - hexdump(len=16): c7 d9 6a fb fa bd 5e 24 8f d7 3b d7 12 5e 38 d6
01-19 17:29:53.676 3182 3183 D C05200/wpa_supplicant: WPS: 1 active PBC session(s) found
01-19 17:29:53.676 3182 3183 D C05200/wpa_supplicant: WPS: attr type=0x104a len=1
...
01-19 17:29:53.718 3182 3183 D C05200/wpa_supplicant: WPS: Received M1
...
01-19 17:29:53.719 3182 3183 D C05200/wpa_supplicant: WPS: Building Message M2
...
01-19 17:29:53.757 3182 3183 D C05200/wpa_supplicant: WPS: Received M3
...
01-19 17:29:53.757 3182 3183 D C05200/wpa_supplicant: WPS: Building Message M4
...
01-19 17:29:53.765 3182 3183 D C05200/wpa_supplicant: WPS: Received M5
...
01-19 17:29:53.767 3182 3183 D C05200/wpa_supplicant: WPS: Building Message M6
...
01-19 17:29:53.774 3182 3183 D C05200/wpa_supplicant: WPS: Received M7
...
01-19 17:29:53.775 3182 3183 D C05200/wpa_supplicant: WPS: Building Message M8
...
01-19 17:29:53.787 3182 3183 D C05200/wpa_supplicant: WPS: Received WSC_Done
01-19 17:29:53.787 3182 3183 D C05200/wpa_supplicant: WPS: Negotiation completed successfully
01-19 17:29:53.787 3182 3183 I C05200/wpa_supplicant: WPS-REG-SUCCESS d2:69:**:**:**:65
...
01-19 17:29:53.903 3182 3183 D C05200/wpa_supplicant: IEEE 802.1X: Force disconnection of d2:69:**:**:**:65 after EAP-Failure in 10 ms
01-19 17:29:53.914 3182 3183 D C05200/wpa_supplicant: p2p0: ap_sta_disconnect STA d2:69:**:**:**:65 reason=23
1.3 四次握手成功及连接成功
01-19 17:29:54.378 3182 3183 D C05200/wpa_supplicant: hostapd_logger: STA d2:69:**:**:**:65 - sending 1/4 msg of 4-Way Handshake
01-19 17:29:54.390 3182 3183 D C05200/wpa_supplicant: hostapd_logger: STA d2:69:**:**:**:65 - received EAPOL-Key frame (2/4 Pairwise)
01-19 17:29:54.391 3182 3183 D C05200/wpa_supplicant: hostapd_logger: STA d2:69:**:**:**:65 - sending 3/4 msg of 4-Way Handshake
01-19 17:29:54.397 3182 3183 D C05200/wpa_supplicant: hostapd_logger: STA d2:69:**:**:**:65 - received EAPOL-Key frame (4/4 Pairwise)
...
01-19 17:29:54.399 3182 3183 I C05200/wpa_supplicant: AP-STA-CONNECTED
01-19 17:29:54.399 3182 3183 I C05200/wpa_supplicant: p2p0: AP-STA-CONNECTED d2:69:**:**:**:65 p2p_dev_addr=d2:**:**:**:81:65
01-19 17:29:54.400 3182 3183 D C05200/wpa_supplicant: hostapd_logger: STA d2:69:**:**:**:65 - authorizing port
01-19 17:29:54.400 3182 3183 D C05200/wpa_supplicant: hostapd_logger: STA d2:69:**:**:**:65 - pairwise key handshake completed (RSN)
01-19 17:29:54.400 3182 3183 I C05200/wpa_supplicant: p2p0: EAPOL-4WAY-HS-COMPLETED d2:69:**:**:**:65
1.4 连接上,大屏设备作为Group Owner
01-19 17:29:54.439 2516 2516 I C04602/sharing: [Sharing][OnP2pConnectionChanged()][wfd_sink_scene.cpp:158] OnP2pConnectionChanged State: 1 (0=Dis, 1=Con), IsGO: 1, GoAddr: 1******1
...
01-19 17:29:54.440 2520 2520 I C05764/ConnWD: [p2p_entity.cpp:35] P2pConnectionChangeCallback# ConnectionState=1, isGroupOwner=1
1.5 上层应用发现并连接上该设备
01-19 17:29:54.552 2516 2651 I C04602/sharing: [Sharing][OnP2pGcJoinGroup()][wfd_sink_scene.cpp:193] Callback Info -> Mac: d******5, Ip: 1******4
01-19 17:29:54.552 2516 2651 I C04602/sharing: [Sharing][OnP2pGcJoinGroup()][wfd_sink_scene.cpp:202] Scanning P2P Device: Mac=d******5, Status=0
01-19 17:29:54.552 2516 2651 I C04602/sharing: [Sharing][OnP2pGcJoinGroup()][wfd_sink_scene.cpp:220] Found NEW device: d******5
...
01-19 17:29:54.556 2516 2651 I C04602/sharing: [Sharing][OnP2pPeerConnected()][wfd_sink_scene.cpp:1343] connected, create sink agent, contextId: 4, agentId: 5, devMac: d2:69:44:22:81:65, devName: wifitest, devIp: 192.168.49.4.
01-19 17:29:54.556 2516 2651 I C04602/sharing: [Sharing][OnP2pPeerConnected()][wfd_sink_scene.cpp:1357] connected, devMac: d******5, devName: w******t, devIp: 1******4.
1.6 上层应用没有成功进行RTSP协商
第1次connecting:
01-19 17:29:55.327 2516 2988 I C04602/sharing: [Sharing][ConnectSocket()][socket_utils.cpp:186] connecting.
01-19 17:29:55.327 2516 2988 D C04602/sharing: [Sharing][CheckAsyncConnect()][socket_utils.cpp:203] trace.
01-19 17:29:57.830 2516 2988 E C04602/sharing: [Sharing][CheckAsyncConnect()][socket_utils.cpp:222] async connect timeout.
01-19 17:29:57.830 2516 2988 E C04602/sharing: [Sharing][Connect()][tcp_socket.cpp:98] connect socket failed, ip: 1******4, port: 7236.
第2次connecting:
01-19 17:29:58.031 2516 2988 I C04602/sharing: [Sharing][ConnectSocket()][socket_utils.cpp:186] connecting.
01-19 17:29:58.031 2516 2988 D C04602/sharing: [Sharing][CheckAsyncConnect()][socket_utils.cpp:203] trace.
01-19 17:30:00.533 2516 2988 E C04602/sharing: [Sharing][CheckAsyncConnect()][socket_utils.cpp:222] async connect timeout.
01-19 17:30:00.533 2516 2988 E C04602/sharing: [Sharing][Connect()][tcp_socket.cpp:98] connect socket failed, ip: 1******4, port: 7236.
...
01-19 17:30:00.533 2516 2988 E C04602/sharing: [Sharing][Connect()][tcp_client.cpp:78] [TcpClient] Connect failed!
01-19 17:30:00.533 2516 2988 E C04602/sharing: [Sharing][StartWfdSession()][wfd_sink_session.cpp:305] sessionId: 6, Failed to connect wfd rtsp server 1******4:7236.
01-19 17:30:00.733 2516 2988 I C04602/sharing: [Sharing][Connect()][tcp_client.cpp:39] peerIp:1******4, peerPort:7236, thread_id: 3056336024.
如上重复5次,然后超时失败。
1.7 随后上层应用主动断开
01-19 17:30:11.351 2516 2988 I C04602/sharing: [Sharing][P2pRemoveClient()][wfd_sink_scene.cpp:1675] p2p remove client: d******5.
01-19 17:30:11.355 3182 3183 D C05200/wpa_supplicant: P2P: Disconnect peer d2:69:**:**:**:65 (iface_addr=0) from group
01-19 17:30:11.359 2211 3201 D C01560/WifiWpaHal: wpa recv buf: IFNAME=p2p0 <3>AP-STA-DISCONNECTED d2:69:44:22:01:65 p2p_dev_addr=d2:69:44:22:81:65!
01-19 17:30:11.359 3182 3183 I C05200/wpa_supplicant: AP-STA-DISCONNECTED
01-19 17:30:11.359 2211 3201 D C01560/WifiWpaHal: wpa p2p callback p :AP-STA-DISCONNECTED d2:69:44:22:01:65 p2p_dev_addr=d2:69:44:22:81:65!
01-19 17:30:47.715 2516 3007 I C04602/sharing: [Sharing][P2pRemoveClient()][wfd_sink_scene.cpp:1675] p2p remove client: d******5.
01-19 17:30:47.720 3182 3183 D C05200/wpa_supplicant: P2P: Disconnect peer d2:69:**:**:**:65 (iface_addr=0) from group
01-19 17:30:47.722 3182 3183 I C05200/wpa_supplicant: AP-STA-DISCONNECTED
01-19 17:30:47.722 2211 3201 D C01560/WifiWpaHal: wpa recv buf: IFNAME=p2p0 <3>AP-STA-DISCONNECTED d2:69:44:22:01:65 p2p_dev_addr=d2:69:44:22:81:65!
01-19 17:30:47.722 2211 3201 D C01560/WifiWpaHal: wpa p2p callback p :AP-STA-DISCONNECTED d2:69:44:22:01:65 p2p_dev_addr=d2:69:44:22:81:65!
01-19 17:31:01.079 2211 3201 D C01560/WifiWpaHal: wpa recv buf: IFNAME=p2p0 <3>AP-STA-DISCONNECTED d2:69:44:22:01:65 p2p_dev_addr=d2:69:44:22:81:65!
01-19 17:31:01.079 2211 3201 D C01560/WifiWpaHal: wpa p2p callback p :AP-STA-DISCONNECTED d2:69:44:22:01:65 p2p_dev_addr=d2:69:44:22:81:65!
01-19 17:31:01.079 3182 3183 I C05200/wpa_supplicant: AP-STA-DISCONNECTED
01-19 17:34:14.136 2516 4080 I C04602/sharing: [Sharing][P2pRemoveClient()][wfd_sink_scene.cpp:1675] p2p remove client: d******5.
1.8 失败根本原因定位
鸿蒙TV在Miracast投屏时失败的主要原因是socket通信失败导致的RTSP连接超时后,上层应用主动去关联:
01-19 17:30:11.346 E C04602/sharing: [Sharing][CheckAsyncConnect()][socket_utils.cpp:222] async connect timeout.
01-19 17:30:11.346 E C04602/sharing: [Sharing][Connect()][tcp_socket.cpp:98] connect socket failed, ip: 1******4, port: 7236.
01-19 17:30:11.346 E C04602/sharing: [Sharing][StartWfdSession()][wfd_sink_session.cpp:305] sessionId: 6, Failed to connect wfd rtsp server 1******4:7236.
结论: 底层的P2P流程正常、连接已经成功建立。失败的直接原因是网络通路不通,上层的SOCKET通信失败导致RTSP交互流程失败,最终超时后上层主动断开连接。
2. 补充测试机型对比分析
- 测试多款手机(小米多款、Redmi K80 Pro、荣耀70)均无问题
- 仅荣耀30系列手机存在该问题(该机型于2020年上市,较老)
- 同厂商的荣耀70无此问题,推测荣耀30可能存在兼容性问题
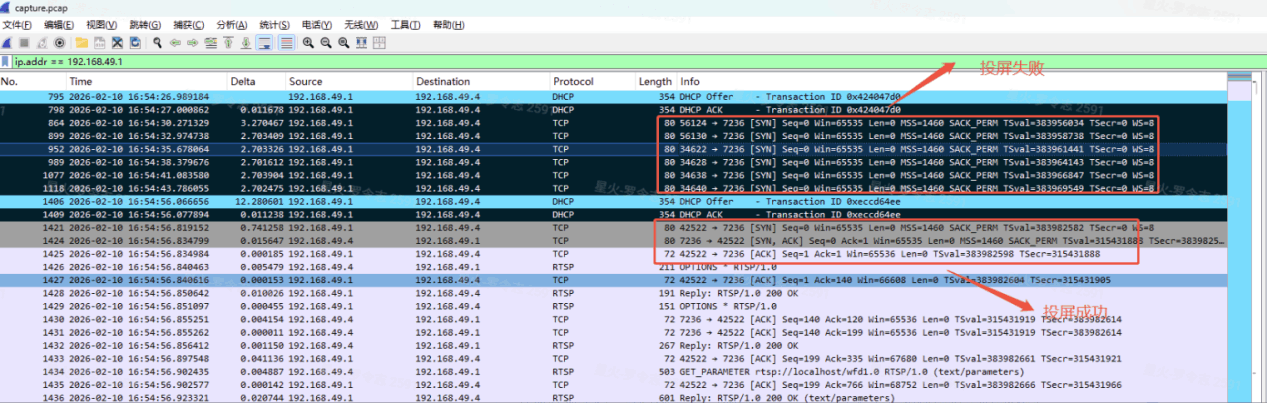
3. 抓包分析(关键)
从tcpdump抓包(capture.pcap)分析:
-- 投屏失败时,大屏发送SYN包(源端口:42522/7236等,目标端口:7236)
-- 荣耀30pro+ 没有回复SYN-ACK
-- 表明TCP连接建立失败,网络层虽通,但手机侧未响应
4.尝试及验证
鉴于仅荣耀30系列(2020年老机型)存在该问题,且测试发现手机连接5GHz Wi-Fi时失败概率更高,推测老款手机对5GHz高频段信道兼容性较差。为验证该假设,将GO信道分别修改为2.4GHz信道1(2412MHz)和5GHz低频信道36(5180MHz)进行测试,结果首次投屏均成功。由此确认,硬编码使用5GHz高频信道149是该问题的根因。
4.1 将GO的信道修改为2.4GHz 2412 MHz(信道1)
-- 测试结果:首次投屏成功
4.2 将GO的信道修改为5GHz 36信道(5180MHz)
-- 测试结果:首次投屏成功
结论: 信道选择对荣耀30系列手机的兼容性有显著影响,使用低频信道可解决首次投屏失败问题。
三、最终解决方案
根因定位
WFD投屏服务(WfdSinkScene)在创建P2P组时,硬编码使用5GHz高频段信道149(5745MHz)。部分老款手机(如荣耀30系列)对该信道兼容性较差,导致手机侧无法正常响应TCP连接请求(SYN包无SYN-ACK响应),最终RTSP连接超时,投屏失败。
解决方案
将硬编码的频段从 5GHz高频信道149(5745MHz) 修改为兼容性更好的 5GHz低频信道36(5180MHz),确保手机侧能够正常建立TCP连接,完成RTSP交互流程。
验证结果
修改后,首次投屏成功率显著提升,问题得到解决。
更多推荐
 已为社区贡献3条内容
已为社区贡献3条内容






所有评论(0)